DryRun Security Now Takes Feedback in Your PR
Security findings have a habit of showing up right when you're about to ship. What follows is always the same: a Slack/Teams thread, someone "checking the dashboard," a debate about whether the issue is real or already handled upstream and a PR that should have merged an hour ago. Possibly and very probably, a bug ticket is filed, and you just blocked a developer and accrued more ticket debt.. great.
PR Feedback cuts that short. When DryRun Security flags something, you respond directly in the PR thread and resolve it there. No context switching. No ticket. No waiting on someone else to clear it.
That's the loop we just closed.
Introducing PR Feedback
When DryRun Security flags an issue in your pull request, you can now reply directly in the PR thread to mark it as a false positive or a nitpick. DryRun removes the finding, regenerates the PR summary, and logs the feedback to improve future scans. No dashboard, no ticket, no waiting.
Why we built it this way
The false positive problem in AppSec isn’t a detection problem, it's a feedback problem. The context that explains why a finding isn’t real lives in a developers head and never makes it back to the scanner, so it flags the same thing again on the next PR.
PR Feedback changes that. Every FP or nit you flag gets logged alongside the original finding and routed into our analysis pipeline, so DryRun gets progressively calibrated to your codebase over time. No config files, no manual tuning. Just a scanner that learns what matters to your team the more you use it.
How it works
When DryRun Security identifies a vulnerability in a pull request, developers can reply directly in the PR thread to mark a finding as a False Positive (FP):
@dryrunsecurity FP [issue ID]
DryRun Security will:
- Analyze the feedback
- Log the feedback for future analysis
- Feed the signal into the system to improve future scans
- Remove the finding from the active list
- Regenerate the PR summary comment
No context switching. No waiting. No tickets. No delays.
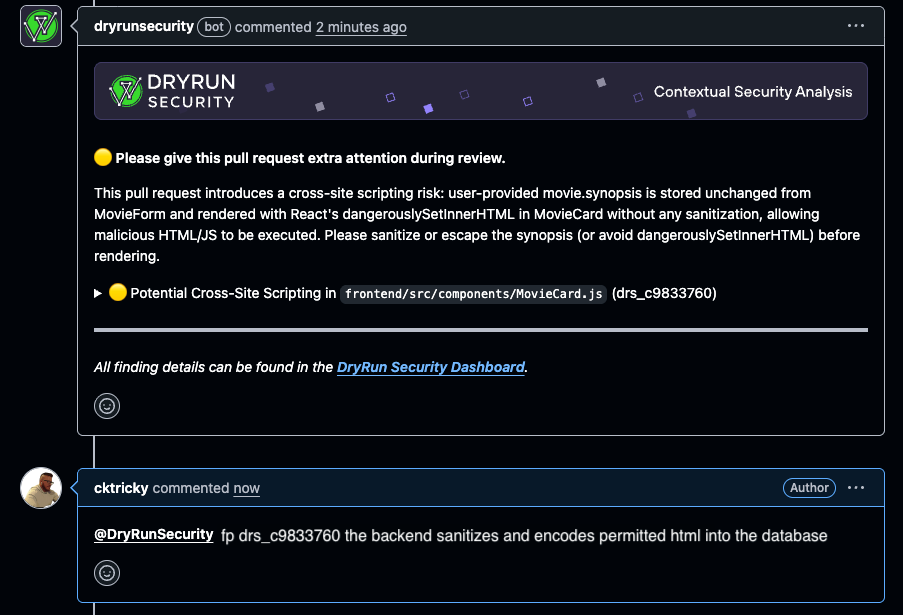
You can also flag nitpicks findings that are technically valid but below the bar your team cares about using the same flow.
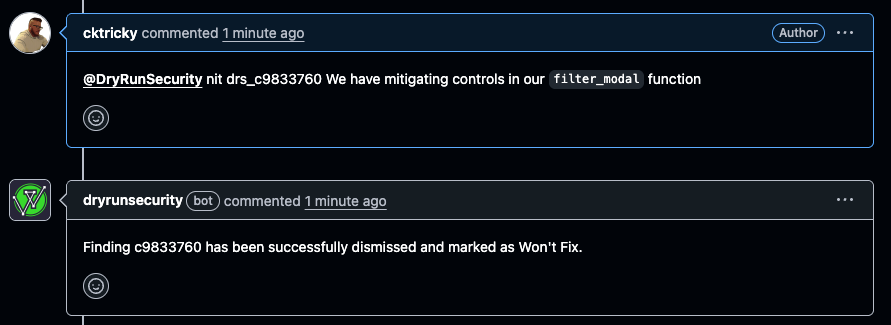
Every action is logged and attributable. A dashboard view for reviewing dismissed findings is coming soon so teams can monitor patterns and step in when needed.
Who this is for
- Developers - If a false positive is blocking your merge and you have context the scanner doesn't, you can act on it without waiting on anyone else. The PR stays unblocked. Your flow stays intact.
- AppSec teams - You get the audit trail. Every FP flagged is logged. When the dashboard view ships, you'll have a single place to monitor what's being dismissed across the org and catch anything that looks off.
- CISOs - Developer velocity and security enforcement don't have to trade off against each other. PR Feedback keeps both intact. Developers move fast. The audit trail keeps it accountable.
Get Started
PR Feedback is live now for all DryRun Security customers. Have questions or feedback on the feature itself? Reach out at hi@dryrun.security
Not a customer yet? Request a demo to see it in action!




