This quarter, the DryRun Security team shipped updates to help you:
- Identify systemic risk across your entire codebase with DeepScan Agent
- Prioritize what actually matters with a centralized Risk Register
- Reduce false positives at the source with PR Feedback
- Enforce security without slowing development using severity-based blocking
- Investigate related vulnerabilities instantly with variant analysis
- See dependency and code risk in one place with SCA in DeepScan
Code is moving faster than security tooling was built to handle. Here's what we shipped in Q1 to close that gap.
Feature Release 01
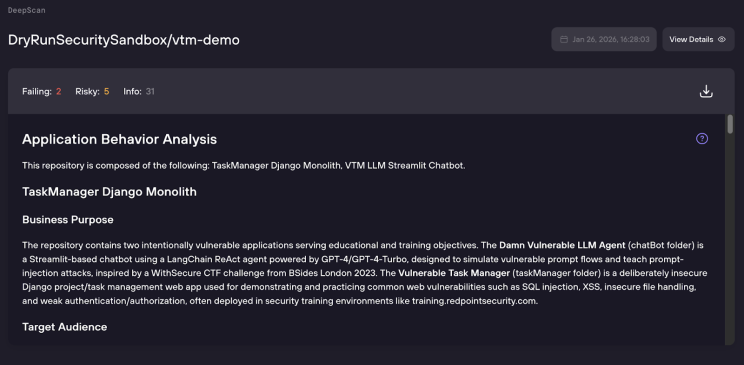
DeepScan Agent: Full-Repository Code Security Intelligence
Security issues do not exist in isolation. They show up in how the application actually behaves across the system.
The DeepScan Agent analyzes your entire repository to understand that behavior. It builds a working model of the application, mapping data flows, trust boundaries, identity paths, and how services interact. From there, it evaluates what the code actually does and how it can be exploited, rather than matching patterns.
That's how it surfaces issues that only exist at the system level. Authorization that breaks across workflows. IDORs that require full data path context. Multi-tenant isolation gaps. Business logic flaws tied to real usage.
DeepScan also brings dependency risk into that same context. SCA findings are now surfaced directly in DeepScan and filterable in the Risk Register. The SBOM endpoint provides a machine-readable component inventory for compliance and supply chain workflows, so application and dependency risk are no longer managed separately.
"DeepScan Agent surfaced more accurate, actionable findings than the $6,000 pentest we had just completed." —Current Customer
Learn more about the Deepscan Agent.
Feature Release 02
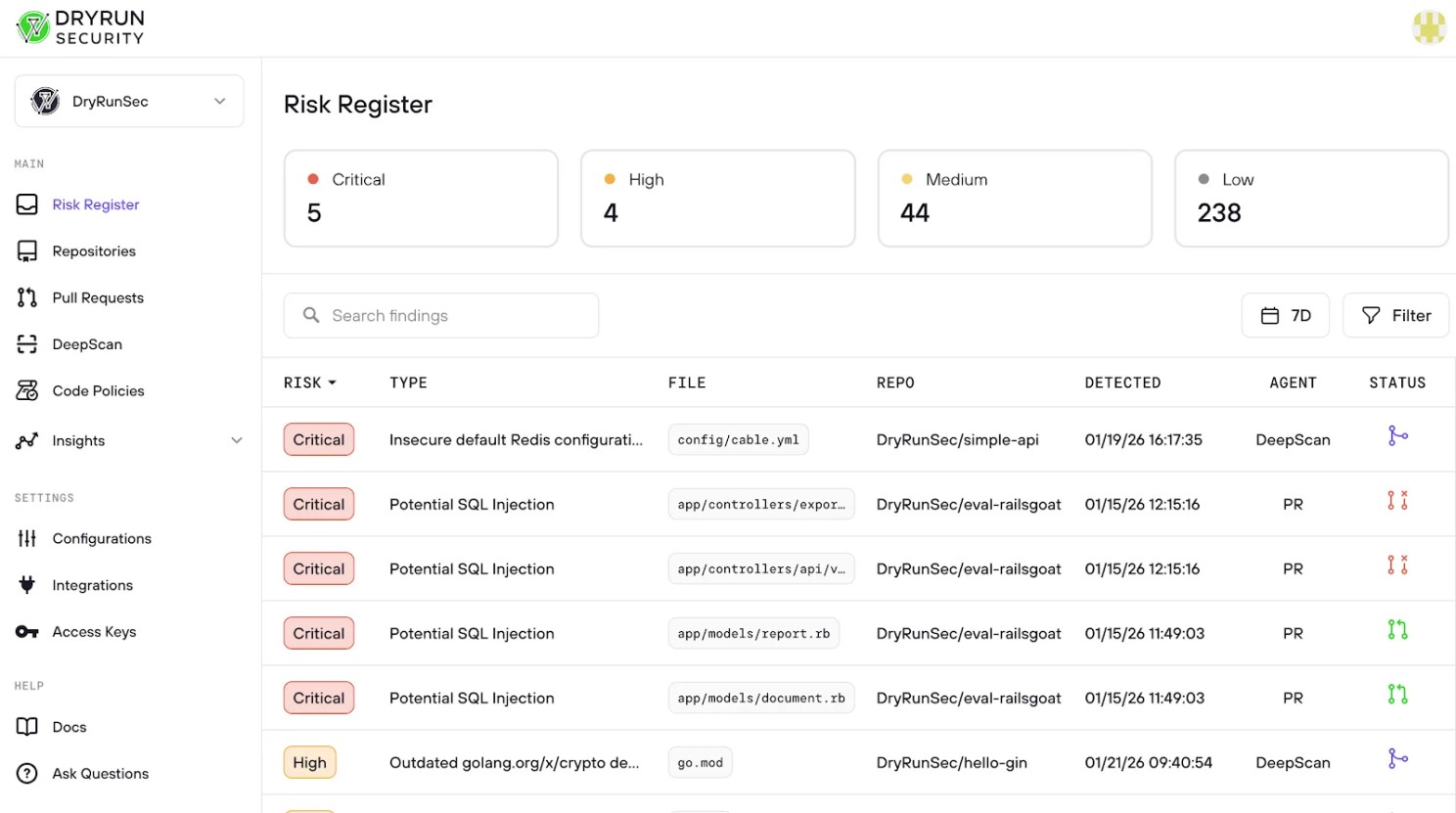
Risk Register: One View Across PRs and Repos
Findings don’t live in one place. They show up in pull requests, across repos, and inside full repo analysis. That fragmentation makes it hard to understand what actually matters, what’s already been handled, and what still needs attention.
Risk Register brings all of that into a single place.
It combines findings from PR scans and DeepScan so AppSec teams can triage, track, and prioritize risk across the entire organization without jumping between tools. It also keeps the context intact. What the issue is, where it came from, how it was handled, and whether it still matters.
What shipped in Q1 for Risk Register:
- Inline finding review with full context so you can triage without leaving the Risk Register
- Dismissed Findings view with a full audit trail of decisions and notes
- Restore dismissed findings to recover anything incorrectly closed
- New dismissal values plus improved logic so “Won’t Fix / Nitpick” decisions reduce repeat noise
- SCA findings now surface in Risk Register alongside code risk
The result is a single place to understand risk across your codebase, not just what was flagged, but what actually needs attention
Feature Release 03
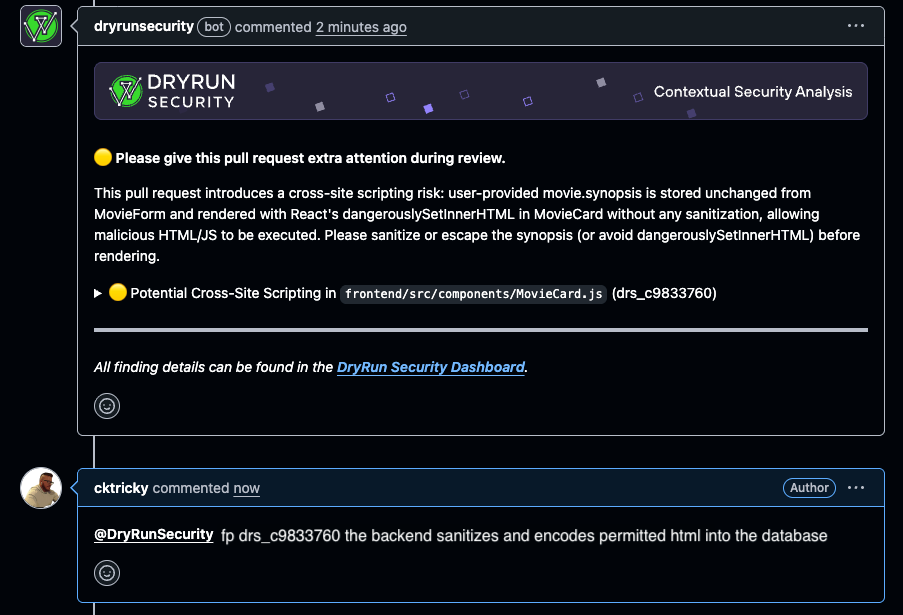
PR Feedback: Close the False Positive Loop
The false positive problem in AppSec is a feedback problem. The context that explains why a finding isn't real lives in a developer's head and never makes it back to the scanner, so it flags the same thing on the next PR. Ticket gets filed, developer gets blocked, the cycle repeats.
PR Feedback cuts that short. Reply directly in the PR thread to mark a finding as a false positive or a nitpick, and DryRun removes it, regenerates the PR summary, and logs it to improve future scans.
@dryrunsecurity fp [issue ID] — no dashboard, no ticket, no waiting
Every feedback response we get is routed into our analysis pipeline. Calibrating scans to your codebase over time without any config file changes or manual rule tuning. Developers stay unblocked. AppSec gets the audit trail. Both happen at the same time.
Platform Improvements Worth Knowing About
Severity Scoring Model (v1)
PR findings are now evaluated based on impact and exploitability, with ratings from Critical to Low. You can also block PRs based on this model, which is a more meaningful control than pass or fail.
MCP via API Access Key
Connect DryRun Security to MCP with an API Access Key instead of OAuth. This is now the recommended method, especially for teams integrating DryRun Security into agentic coding environments. Setup instructions are on the Integrations page.
Revamped Insights Page (Beta)
Inline AI assistant with streaming responses, redesigned cards with expandable sections, quick question suggestions, and a Category Manager. It’s an early version of what we expect to become the primary surface for AppSec teams who want to ask questions about risk rather than just read dashboards.
SCM Comment Visibility Toggle
Configure whether DryRun Security comments on every scanned PR or only when findings are present. Removes the ambiguity of silence for teams who want confirmation that every PR was reviewed.
Notification Deduplication
Duplicate notifications are now suppressible when risk level hasn't changed on a PR.
GitLab Install All now respects project hierarchy.
Group installs propagate correctly through the project structure.
Try it for yourself.
Log in to your DryRun Security account to try out these new features today. If you're not a customer yet and want to learn more, request a demo.
As always, we welcome your feedback. Let us know what you think by reaching out to us at hello@dryrunsecurity.com and stay in the loop on DryRun Security news on LinkedIn.



